From Synthetic Tests
to Real Malware
Lab 010 documented how Ladon was built — the detection modules, the architecture decisions, the scoring logic. It ended with a straightforward observation: synthetic test files tell you the code runs. Real malware tells you the detection logic actually works. This lab is that test.
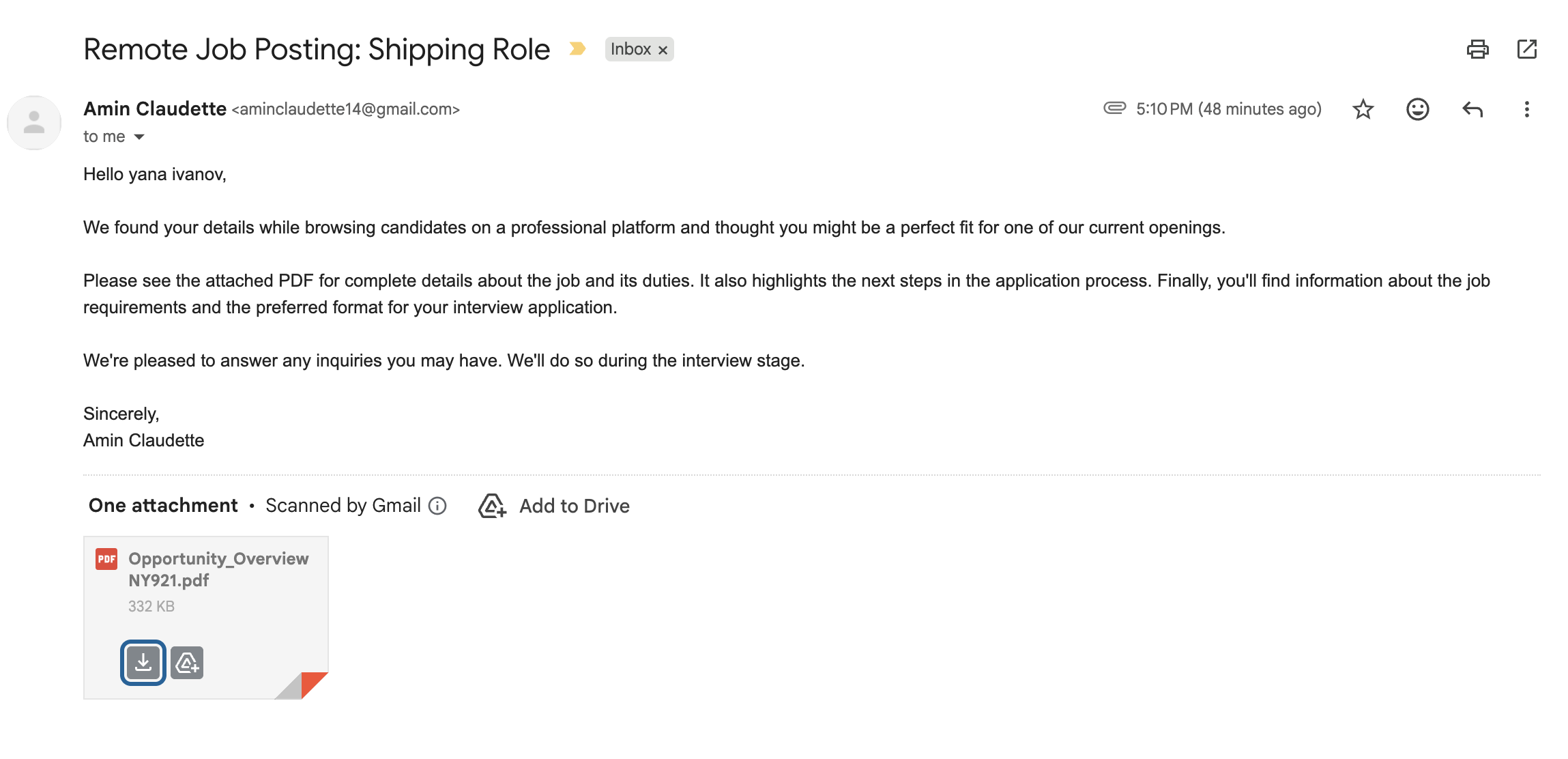
The five samples analyzed here were sourced from MalwareBazaar and one live phishing attempt that arrived in my own inbox. All five are PDFs. All five triggered Ladon's polyglot detection module. None of them were safe to open.
The goal of this lab is not to reverse-engineer the malware — Ladon is a triage tool, not a malware analysis platform. The goal is to document what the tool found, what those findings mean, and what would have happened to a non-technical user who opened any of these files.
On sample handling: All analysis was performed using Ladon's static analysis engine. No file was executed, opened in a PDF viewer, or processed by any renderer. Ladon reads raw bytes only. Four samples were sourced from MalwareBazaar. One arrived as a live phishing email. Hashes are included for reference. The files themselves are not distributed.
The Samples — What Ladon Found
Each sample is presented with its Ladon report findings, what those findings mean in practice, and what a non-technical user would have experienced if they had opened the file.
.msi and .exe hosted on Tencent Cloud, active at time of analysis. Direct links to secondary payloads on cos.ap-guangzhou.myqcloud.com, including lnstaller.msi — deliberate misspelling of "installer" to evade string-based detection./AA key triggers code execution automatically on page open, page close, or document print — no user interaction required beyond opening the file.maneger-accouintr-solutieonst.site — Deliberate misspelling of "manager account solutions" on a .site TLD. A throwaway phishing domain designed to pass a visual scan.MZ header) embedded inside a structurally valid PDF. Opens and renders normally in any viewer. No file extension or header-only scanner will find the payload.This is the sample that validated the intended use case for Ladon — a real phishing email, a real target, a payload that passed Gmail. Ladon caught it on first scan.
The Pattern Across All Five
Every sample in this set is a polyglot. That is not a coincidence — it is a reflection of how effective the technique is. A PDF that contains a Windows PE executable will pass file extension checks, pass magic byte checks, open normally in any PDF viewer, and show readable content to the recipient. The executable is not visible. It makes no noise. The only way to find it is to scan the entire file for secondary signatures — which is exactly what Ladon does.
| Sample | Attribution | Severity | PE Offset | Additional Findings |
|---|---|---|---|---|
| d67e62bb… Unknown dropper |
Unknown | HIGH | 36,700 | /ObjStm — hides objects from scanners |
| e2b75bae… ValleyRAT / SilverFox |
Chinese APT | CRITICAL | 4,937 | /URI ×20, live Tencent Cloud .msi + .exe C2 |
| b046d04b… Facebook phishing |
Unknown | CRITICAL | 18,238 | /AA ×6 auto-execute, /URI ×4, typosquatted .site domain |
| 5095c647… Gamaredon loader |
Russian APT (FSB) | HIGH | 18,385 | None — clean PDF layer |
| Opportunity_ Job scam · live catch |
Unknown | HIGH | 10,303 | None — clean PDF layer |
Three of the five samples would have been entirely missed by a scanner that only checks PDF structure. Two would have been partially flagged — the auto-execute actions and suspicious URLs in samples 2 and 3 would have triggered something. But the embedded executable in every case would have gone undetected without a full-file secondary signature scan.
On the clean PDF layer in samples 4 and 5: The absence of active PDF content is worth noting. An attacker who embeds a PE executable and adds no JavaScript, no auto-execute actions, and no suspicious URLs produces a file that is specifically harder to detect — it generates no behavioral signals, no network callbacks, nothing that heuristics can catch. Cleaner PDF structure is not a sign of a less dangerous file. The Gamaredon sample makes this point with state-sponsored precision.
What This Validates About Ladon
The detection methodology in Ladon was built from reading threat reports and file format specifications. These five samples are the first test against files that weren't constructed to test the tool. The results hold.
Every sample triggered the polyglot detection module correctly. The severity scoring separated the two CRITICAL samples from the three HIGH samples. The URL analysis module correctly flagged the live Tencent Cloud C2 URLs in sample 2 and the typosquatted domain in sample 3. The PDF structure module correctly identified the auto-execute actions in sample 3 and the object stream obfuscation in sample 1.
The live phishing sample is the most meaningful data point. It was not sourced from a malware repository. It was not constructed to test anything. It was a real phishing email sent to a real target. Gmail did not flag the attachment. Ladon caught the embedded PE at offset 10,303 on the first scan.
The intended use case, validated: Ladon was designed for a specific scenario — a non-technical employee at a defense contractor or small business who receives an unexpected PDF and has no way to know if it is safe to open. The job scam email is exactly that scenario. The file looked like a PDF, opened like a PDF, and passed Gmail's scanner. The only thing that identified it as malicious was reading the raw bytes — which is exactly what Ladon does, automatically, before anyone opens anything.
Detection Improvements — April 30, 2026
Following the original publication of this lab, two issues were identified through continued testing and addressed with updates to document_triage.py. Both fixes are documented here with validation results.
The problem: Ladon's polyglot detection was producing false positives on large legitimate PDFs — corporate threat intelligence reports, technical manuals, and similar documents were occasionally triggering a CRITICAL finding when no malicious content was present. The issue was specific to files with heavily embedded binary content such as fonts, images, and color profiles.
The fix: The PE detection logic was updated to require a higher confidence threshold before flagging a finding. A file must now satisfy multiple structural validation checks before a Windows executable signature is reported. Incidental byte patterns that are not part of a real executable no longer trigger the module. The change was validated against both clean and malicious samples to confirm zero false negatives.
Re-test output — 2026-04-30 21:24 UTC
File: e2b75baeb7ed21fb8f27984f941286770d1c3c0b60fce8d7fa5b167bd24ba6dc.pdf · 158.4 KB · Severity: CRITICAL
Polyglot Detection — 1 finding
[CRITICAL] Windows PE (EXE) signature found at offset 4937 inside PDF file
PDF Structure Analysis — 6 issues
[Critical] /URI detected (20×) — External URI reference
[Warning] https://6-1321729461.cos.ap-guangzhou.myqcloud.com/lnstaller.msi
[Warning] https://00-1321729461.cos.ap-guangzhou.myqcloud.com/24-12-13uninstall.exe
[Warning] http://www.baidu.com
URL Analysis — 13 suspicious URLs
Tencent Cloud COS domains (cos.ap-guangzhou.myqcloud.com) flagged MEDIUM — live Chinese APT C2 infrastructure confirmed at time of original analysis. Note: URL scoring for Chinese cloud infrastructure is a known improvement area — these domains warrant CRITICAL given attribution context.
The problem: Ladon's calendar invite analysis was incorrectly flagging two categories of legitimate calendar invites as CRITICAL meeting platform spoofs. Invites scheduled through third-party scheduling platforms were being flagged because they reference meeting platform names without routing directly through those platforms. Additionally, calendar invites forwarded through corporate email security gateways were being flagged because those gateways rewrite URLs before delivery, making a legitimate Zoom or Teams link appear to come from an unrecognized domain.
The fix: The calendar analysis module was updated to recognize both categories correctly. Legitimate scheduling platforms and known corporate email security gateways are now handled appropriately, passing clean instead of triggering false spoof alerts. Actual attacker-controlled domains that impersonate meeting platforms — the core detection target — are unaffected and still trigger CRITICAL.
On the BlueNoroff campaign context: The fake Zoom test case was modeled on a documented active campaign. Arctic Wolf reported in April 2026 that BlueNoroff — a Lazarus sub-group tied to North Korea's Reconnaissance General Bureau — was using Calendly invites that later swap to typosquatted Zoom or Teams links to deliver second-stage malware via a fake SDK update prompt. The campaign was independently covered by GovInfoSecurity, Dark Reading, Infosecurity Magazine, and CyberSecurityNews between April 17–28, 2026, and is tracked under UNC1069 and Sapphire Sleet. The fix correctly allows legitimate Calendly scheduling through while catching the attacker-controlled destination domain substitution.
Active Campaign IOCs — April 2026
The following indicators are documented in ThreatFox (community submissions dated April 8, 2026) and are consistent with the BlueNoroff/UNC1069 fake Zoom campaign. Domains are defanged — brackets replace dots to prevent accidental navigation. These domains would trigger Ladon's ICS analysis if embedded in a calendar invite LOCATION or DESCRIPTION field.
| Defanged Indicator | Type | Pattern |
|---|---|---|
| usz00mczyiee[.]store | DOMAIN | Zero substitution in "zoom" — usz00m vs zoom |
| zoominviteeees[.]de | DOMAIN | Extra characters appended to "zoom" + unusual TLD |
| googlemeet[.]emilychart[.]xyz | DOMAIN | "googlemeet" as subdomain of unrelated domain + .xyz TLD |
| simplicity-w[.]pages[.]dev | URL | Cloudflare Pages abuse — legitimate infrastructure, malicious content |
What Ladon catches vs. where its boundary is: If any of these domains appeared in a calendar invite LOCATION or DESCRIPTION field, Ladon would flag CRITICAL — suspicious TLD, platform keyword in wrong domain, or typosquat pattern. What Ladon does not catch is the browser-based payload delivery stage: the fake meeting room rendering pre-recorded video, the fake audio failure, and the ClickFix "SDK Update" prompt that delivers the actual malware. That stage happens in the browser after the user clicks the link. Ladon is a pre-click triage tool — it catches the lure before it is opened. Detecting the browser-based stage requires endpoint behavioral detection or DNS-layer blocking, not static file analysis.
All five original malicious samples were re-tested after both fixes. Zero false negatives — every confirmed malicious file still fires at the correct severity. Zero false positives introduced — clean files that previously triggered incorrectly now pass clean.
The Full Picture
Across both the original analysis and the April 30 improvements, Ladon's detection posture is zero false negatives on confirmed malicious files and zero false positives on the clean files tested. The PE validation fix closes the most common source of noise for users who scan large corporate documents. The calendar fix closes the most common source of noise for users who scan calendar invites from scheduling platforms or corporate email environments.
The tool does not execute anything. It does not require network access. It reads raw bytes and reports what it finds — which is exactly what is needed before anyone opens an unexpected file.